Configure Network for Private Access to Google APIs and Services
If you deploy a CelerData cluster in a private subnet for security reasons, the cluster, by default, cannot not be accessed or access resources over the public internet, including Google APIs and Services. However, CelerData Cloud requires access to Google APIs and services to:
- Download installation packages from your VPC when deploying a cluster.
- Store data for Elastic clusters.
- Upload query profiles to Google Cloud Storage.
To enable private access to Google APIs and services, you must configure a Cloud DNS zone, create routes, and set up a firewall rule as described below.
If you want to enable Shared VPC for the cluster, you need to follow the instructions provided in Set up Shared VPC to set up a Shared VPC. The VPC network, subnet, firewall rules, Routes, and Public Cloud NAT (or reserved internal static IPv4 address) you used for deployment must belong to the host project of the Shared VPC.
Create a Cloud DNS Zone
To configure a private DNS zone for Google APIs, follow these steps:
Follow these steps to create a private Cloud DNS zone:
- Sign in to your project in the Google Cloud console.
- Expand the left-side navigation menu, and choose Network Services > Cloud DNS.
- Click CREATE ZONE.
- On the Create a DNS zone page, follow these steps:
- For Zone type, select Private.
- Enter a Zone name, for example,
google-private-access. - For DNS name, enter
googleapis.com. - In the Network section, click ADD NETWORKS. In the New networks box, select your Project and choose the VPC Network for cluster deployment, and click DONE.
- Click CREATE.
After creating the DNS zone, add an A record and a CNAME record to the private Cloud DNS zone:
- From the zone detail page, click ADD STANDARD to create an A record:
- For DNS name, enter
private. - For Resource record type, select A.
- For IPv4 Address, enter four IP addresses:
199.36.153.8,199.36.153.9,199.36.153.10,199.36.153.11 - Click CREATE.
- For DNS name, enter
- Click ADD STANDARD again to create a CNAME record:
- For DNS name: Enter
*. - For Resource record type, select CNAME.
- For Canonical name, enter
private.googleapis.com. - Click CREATE.
- For DNS name: Enter
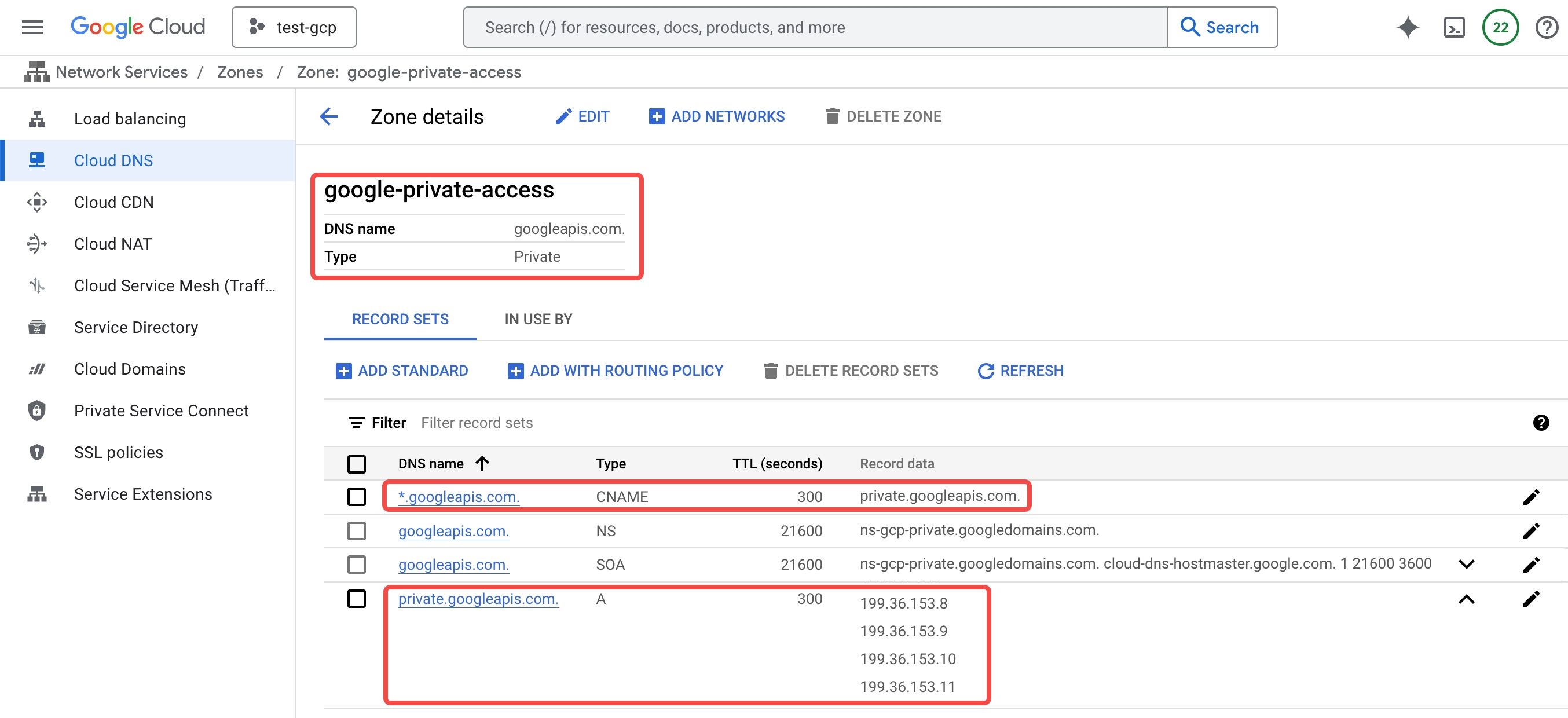
For more details, see Configure DNS for googleapis.com.
Create Routes
To allow traffic to Google APIs and services, follow these steps to configure routing rules:
- Sign in to your project in the Google Cloud console.
- Expand the left-side navigation menu, and choose VPC Network > Routes.
- On the ROUTE MANAGEMENT tab of the Routes page, click CREATE ROUTE.
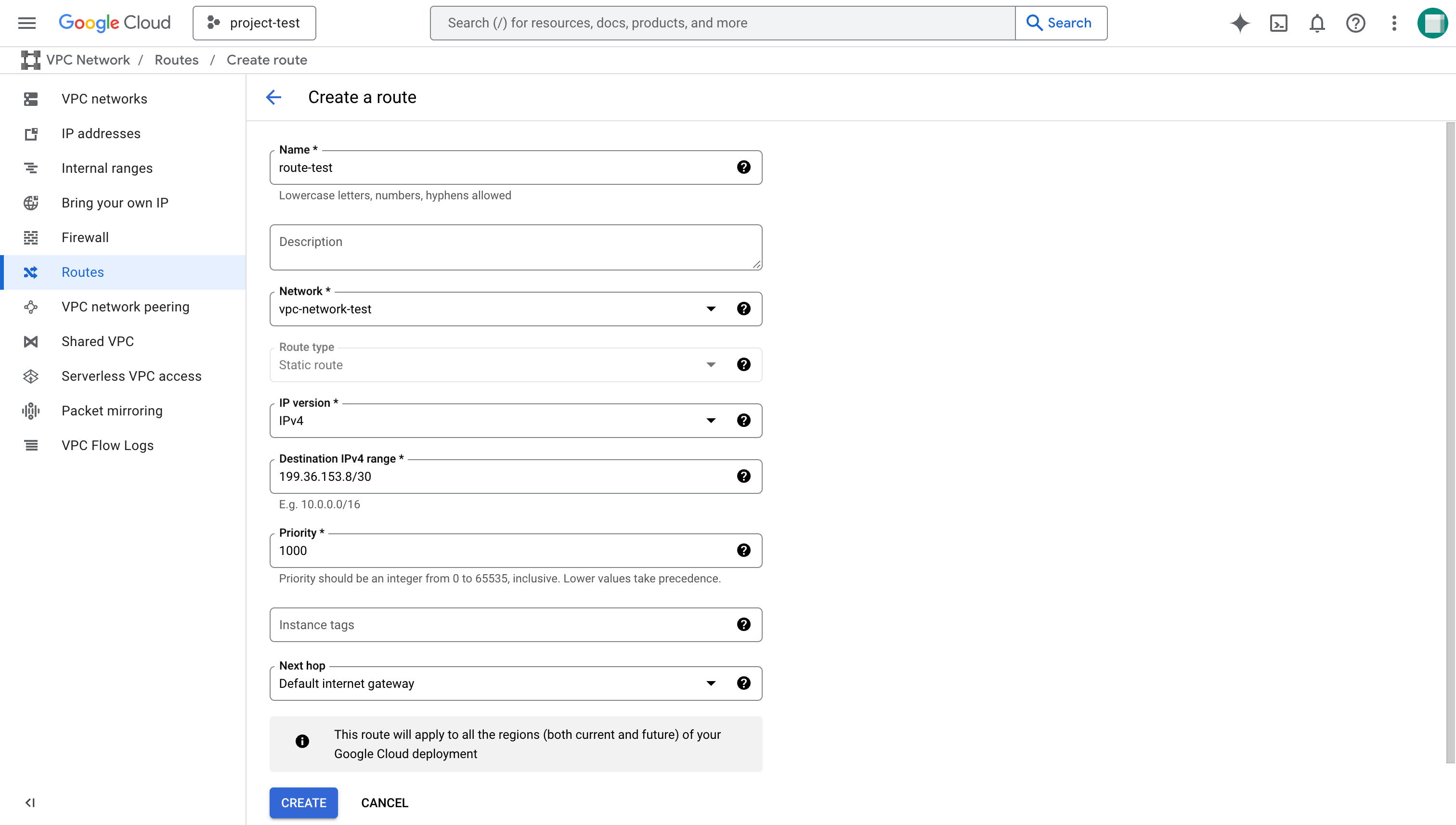
- On the Create a route page, follow these steps:
- For Name, enter a name for the route.
- For Network, select the VPC for cluster deployment.
- For Destination IPv4 range, enter
199.36.153.8/30. - For Next hop, select Default internet gateway.
- Click CREATE.
- Repeat the above procedure to create a second route with Destination IPv4 range set to
34.126.0.0/18.
Add a firewall rules
To allow traffic to Google APIs, you also need to add an egress firewall rule:
- Sign in to your project in the Google Cloud console.
- Expand the left-side navigation menu, and choose VPC Network > Firewall.
- Click Create firewall rule.
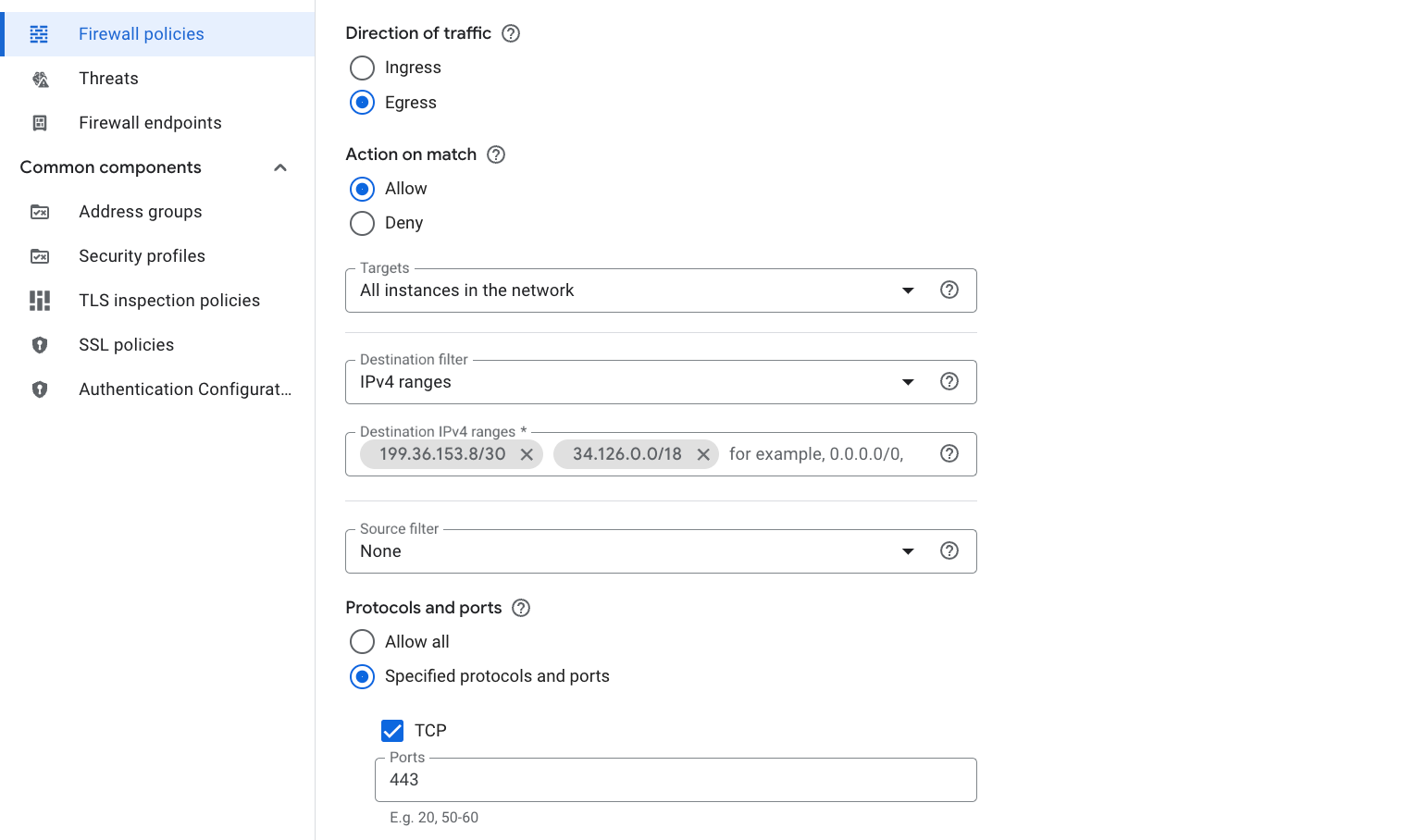
- On the Create a firewall rule page, follow these steps:
- For Name: Enter a name for the rule, for example,
fr-egress-google-private. - For Network, select the VPC for cluster deployment.
- For Direction of traffic, select Egress.
- For Targets, select All instances in the network.
- For Destination IPv4 ranges, enter
199.36.153.8/30and34.126.0.0/18. - For Protocol and ports, select Specified protocols and ports, choose TCP, and enter
443.
- For Name: Enter a name for the rule, for example,
- Click Create.
For more details, see Configure Private Google Access.
Summary
After completing these steps, your CelerData cluster can:
- Download installation packages during deployment.
- Store and retrieve data from Google Cloud Storage.
- Upload query profiles securely.
This setup ensures private access to Google APIs and services without exposing your cluster to the public internet.